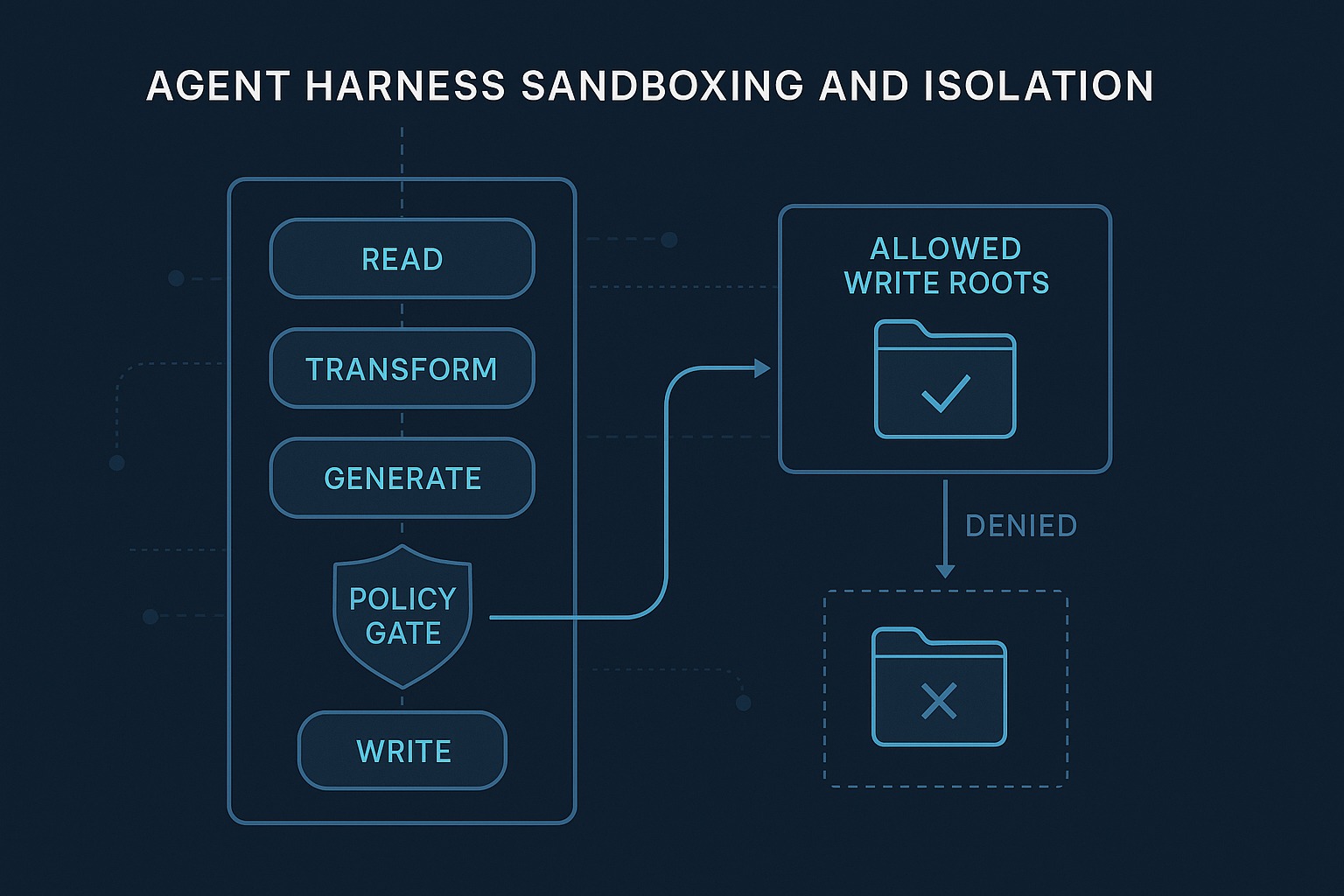
Sandboxing, Isolation, and Safe Execution
The live demo repo for this series is 67ailab/harness-engineering, and for this post I did change the repo before publishing. The new capability shipped in commit 98c6302, which adds an explicit policy layer to the harness: tools now carry action categories, risky writes are checked against allowed output roots before execution, and policy decisions are persisted in traces and summaries. The key code changes are in: src/harness_engineering/policy.py src/harness_engineering/tools.py src/harness_engineering/runner.py src/harness_engineering/cli.py src/harness_engineering/mcp.py src/harness_engineering/tracing.py src/harness_engineering/store.py src/harness_engineering/workflow.py sample_data/policy/restrictive.json That matters because “sandboxing” gets used too loosely in agent conversations. Sometimes people mean a real OS sandbox. Sometimes they mean a container. Sometimes they mean “the model only has a few tools.” Those are not the same thing. ...